As published in the The Cutting Edge by the Santa Clara County Dental Society
Technology Disaster Preparedness
You’ve invested time and money in your business and your technology. Now is the time to put measures in place to protect those investments – not after a disaster happens. You wouldn’t install a fire alarm or talk to your kids about an escape plan after you’ve had a fire. So why would you wait to establish a disaster plan after you’ve had a disaster?
In today’s digital age, our technology is the base of our businesses; without it, how much of your day-to-day would you be able to do successfully? Now, think about losing all that technology, and information housed in that technology, due to fire, flood, earthquakes, theft, employee negligence, vendor error, cyberattacks, or ransomware. What is your plan?
The following are some ideas of the concerns we face daily. I urge you to review them and put a plan in place that makes sense for you and your organization. Disaster preparedness is not a one-size-fits-all solution, and every business has its protocol of importance.
Deferred Maintenance:
Deferred maintenance is one of those things you don’t think can truly “hurt” your practice. This isn’t a disaster, is it? Ignoring your technology maintenance and replacement schedule will creep up on you and quickly make itself a priority. If your computers crash and you can’t take X-rays, schedule patients, or accept payments, that is an emergency. Also, consider the long-term costs of lost productivity from slow computers and network equipment. Sometimes that can add up to more over the years than the cost of proactive, scheduled replacement.
Deferred maintenance also creates cybersecurity vulnerabilities. You may have heard that Microsoft is no longer providing support or updates for Windows 7 or Server 2008 as of January this year. Those updates, or patches to security, are a crucial component of your security posture. Without those updates, you open the door for your network to ransom in a cyberattack. So, how much money are you saving by deferred maintenance, as compared to ransom payments, practice downtime, and potential HIPAA fines?
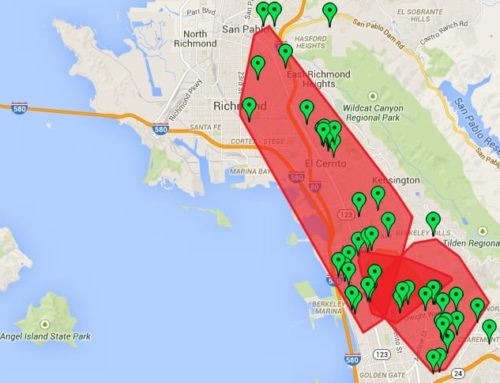
Natural Disasters
Living in California, we expect and should prepare for natural disasters, such as fire, flood, and earthquake. As these environmental factors change, we must adapt in our ability to prepare for them so your business can survive financially intact.
Public Safety Power Shutoffs (PSPS):
Businesses are being impacted by PG&E’s recent process for minimizing damage to life and property by wildfires. There are several factors in this situation:
- Are you under evacuation?
- Do you have a generator?
- Is your staff able to come in?
- Will your patients cancel because they don’t have power?
- Will your insurance cover this kind of downtime claim repeatedly?
Your answer to each of these unknowns will determine how you customize your Disaster Preparedness Plan.
Theft:
Physical theft of servers and paper charts is still a problem for smaller practices. We’ve all seen it, the boarded-up door or window because it was smashed in a burglary. Why would someone break into a practice? The same reason they hack into your system. Data is King. It’s old school, but it still works, so it still happens. It is important to lock up servers and computers, as well as those who have paper charts. Encryption of servers and backup drives are yet another way to keep clear of any potential data breaches that could close your practice. Yes, you locked your server, but if it was stolen and not encrypted, you may lose your clients’ trust, and that means your business.
Employee Error/Malicious Employee:
At some point, every business will experience data loss or data corruption from an errant or malicious team member. Whether accidental or intentional, you must prepare. How? Education is key to those employee errors. Training on what a phishing email looks like and reminders not to click on attachments that they are not expecting. Even more so, with spoofing emails, we must be vigilant in looking for what the email is requesting and deciding whether it’s a normal request. If there is a question, ask!
Maliciousness isn’t something you can plan for; we all expect our employees to be good-hearted. Unfortunately, that isn’t always the case. In this situation, a good backup is essential.
Vendor Error/Ignorance:
Part of any solid Disaster Preparedness Plan must include Business Associate Agreements (BAA) with your vendors. According to a CynergisTek report, “Third-party vendors working with healthcare provider organizations accounted for more than 20 percent of breaches in the healthcare sector last year.” In fact, the same research noted that vendors are responsible for some of the largest breaches to date. If you signed a generic BAA provided by your vendor, there is a good chance you would be left to manage and mitigate and problems. You would be bearing the financial and physical brunt of something that was not your fault. Except it was if you didn’t thoroughly review or even have a BAA. (Click Here for a free White Paper on Business Associates.)
Ransomware:
Ransomware is a type of computer virus that encrypts and locks all your files and holds your data for ransom. Your business should prepare for this common problem and never be in a position to have to pay the ransom. Ransomware can make it into your systems in any number of ways: employee error, open ports, or unpatched systems, like Windows 7 or Server 2008.
The best way to combat this issue is before it becomes a problem. Train your employees, have a solid firewall in place, and plan for a failure. Ransomware is going to happen at some point. How quickly you can react makes all the difference. When the ransomware gets in, you need to know you have a solid, trusted, and tested backup. A trusted backup allows you to return to a point in time before the ransomware. You will be able to carry on business without succumbing to paying the ransom. Your data loss and practice downtime will depend on the type of backup you have (See below).
Backups:
Backups come in all flavors and colors these days. Cloud backups versus on-premise, file-based versus image-based. It all depends on your preference. What is an acceptable recovery time for you? What is acceptable downtime for your practice, should the worst happen? All have their pros and cons. On-premise is less expensive but can be stolen or damaged beyond repair along with your server and workstations. Image-based can have you up and running in a matter of hours versus the filed-based in a matter of days. What is your organization’s tolerance for getting back to producing after the worst happens?
Making a Disaster Plan
Now that you know you need a Disaster Plan, how do you go about making one? Just like writing, you have to answer the who, what, why, where, and when; when writing your Disaster Plan, you must Identify, Protect, Detect, Respond, Recover, and Test/Repeat.
You must identify each issue, state how you are going to protect it, detect how the disaster would affect the practice, describe how you will respond, and then recover from the incident. Lastly, one of the most important aspects that most people forget is to TEST and repeat the process. Having a plan won’t help if it doesn’t work when you must use it after the disaster has occurred.

Heading up the Compliance and Risk Management Division at ACS, Amy Wood consults with healthcare practitioners and Business Associate vendors, both before and after a Data Breach. She helps minimize the damage after a data breach and implements proactive compliance programs into existing workflows.
Amy also provides CE presentations to practices and clinics, dental associations, study clubs, and disability groups as well as to vendors and Business Associate practices. She can be reached at [email protected]